Where does Section IV fit into the Cyber Division and where does the Cyber Division fit into the rest of the FBI?
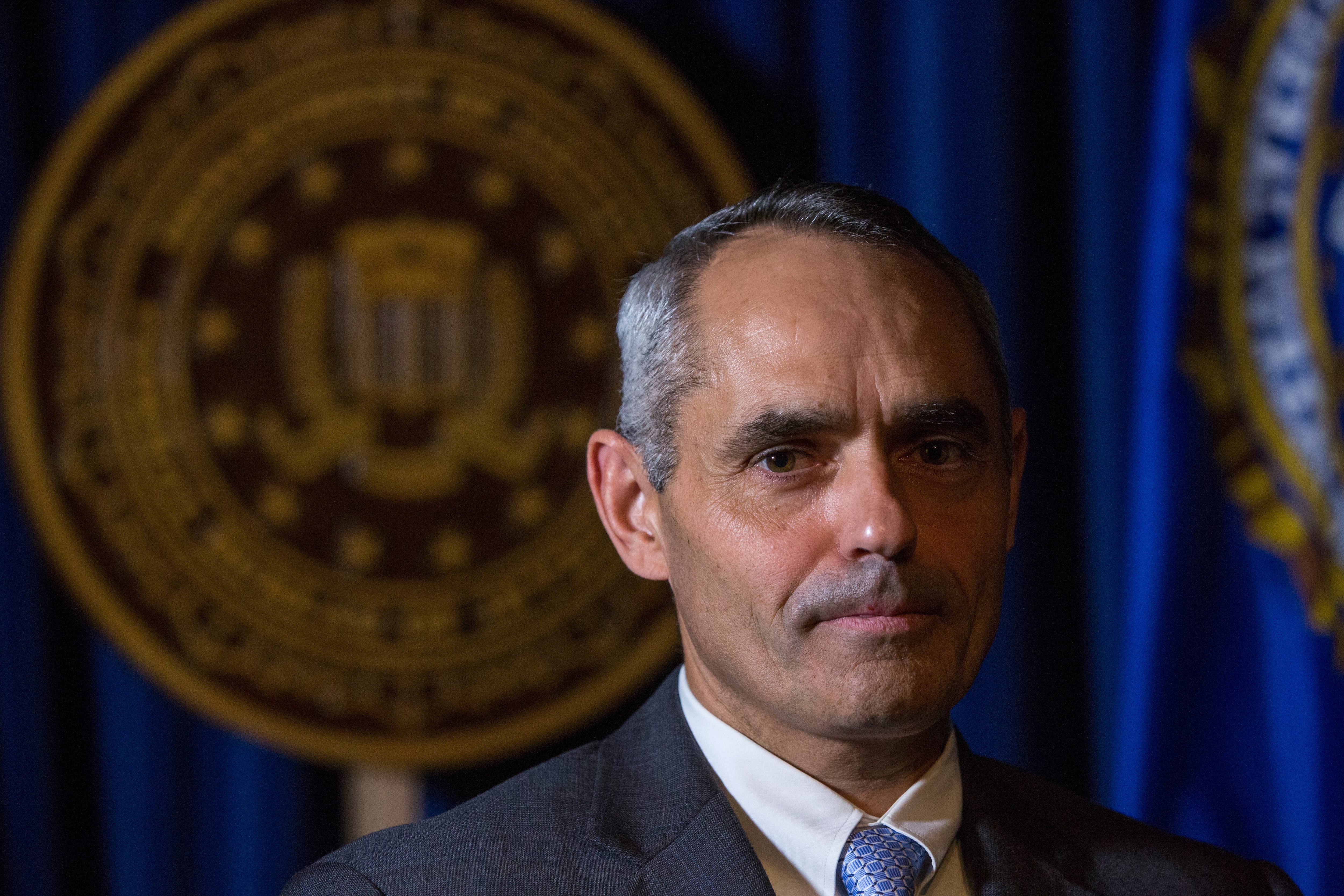
The Cyber Division has five operational sections. I'm the chief of Section IV and we focus on operational coordination and technical operations.
For operational coordination, there's a lot to make a huge division — like cyber division — move forward. We manage the strategy management piece.
We also deal with our overseas partnerships. The FBI has attaché offices in 75 embassies around the world. And in a number of those we have cyber special agents positioned to work with our international partners.
And then we develop tools and techniques that can be used to counter cyber intrusions.
For the FBI the mission of the Cyber Division is to identify, pursue and defeat cyber adversaries wherever they come from. We are one of the FBI's operational divisions similar to the criminal division or the terrorism division.
The Cyber Division is the lead domestic cyber investigative agency. We focus on national security threats, we focus on criminal threats effecting our banking industry, retail industry, private corporations — so we work the whole gamut.
We utilize a whole of government approach. There are many federal agencies who have a piece of the cyber portfolio and we partner with all those agencies. As a matter of fact the FBI Cyber Division hosts the National Cyber Investigative Joint Task Force, which is an FBI-led agency mandated by presidential directive to be the lead coordinating agency for all cyber investigations. And then we partner with the Department of Homeland Security and many other agencies within the intelligence community to combat the cyber threat.
![Program View: History of FBI Cyber Division [ID=74871426]](/Portals/_default/Skins/PrestoLegacy/CommonCss/images/smartembed.png) What are the trends that you're seeing in intrusions? What's new in breeches and what are the kind of things that are standing the test of time?
What are the trends that you're seeing in intrusions? What's new in breeches and what are the kind of things that are standing the test of time?
What has stood the test of time is the human factor. Spear-phishing emails are very, very popular and they will continue to be popular. People will continue to target the human factor involved with computer systems, whether it be for government agencies or businesses.
In terms of new trends, as we expand our ability to conduct business via mobile apps, smart phones, remote accessing into an individual's place of employment and their computer systems the bad guys, the cyber adversaries are expanding their ability to target those mobile systems. It's a factor as technology evolves and more and more people become more and more mobile in how they learn, how they conduct business, how they do their banking. It presents a whole new target of opportunity for the cyber adversaries to target those applications.
How does a cyber investigation work?
Two ways. A company may notice some unusual activity on their own network or they might get a notification from their local cyber taskforce that we believe there are some unusual things occurring on their network. From there a dialogue begins in most cases.
Companies have no obligation as the victim to work with law enforcement, so we truly see it as a partnership. We actually call it our Sony model, modeled after the Sony investigation where we were in full partnership with the victim.
All too often in a bank robbery or carjacking people are very happy to see law enforcement respond or the FBI. "Thank God you're here; this is what the bad guy or bad girl looked like."
In the case of cyber intrusions they're not so sure if they're happy to see you or not. And they usually have to make up their mind as to whether or not they do or don't want to work with you. Because, again there is no obligation on the part of the victim to work with law enforcement.
They may not want to work with law enforcement because they're afraid of being exposed publically that there was a computer intrusion on their network. Depending on what industry they're involved in there are certain regulatory requirements for reporting to government agencies. However, if there's an ongoing law enforcement investigation there are authorized delays in those reporting requirements, which could potentially be an advantage of notifying the FBI or another federal law enforcement agency of the cyber intrusion.
![Program View: How cyber differs from traditional investigations [ID=74871512]](https://presto-federaltimes.gannettdigital.com/Portals/_default/Skins/PrestoLegacy/CommonCss/images/smartembed.png) What are the first steps the FBI takes in an investigation?
What are the first steps the FBI takes in an investigation?
We're going to notify the appropriate field office. If it's a headquarters for a federal agency here in Washington, we're going to notify our Washington cyber taskforce. We're going to make sure that the Department of Homeland Security cyber center is aware of the computer intrusion. Then we're going to find out who the point of contact is.
Then, we're going to conduct interviews — physical, old fashioned interviews with the people that first noticed the cyber intrusion. We're going to try to identify the initial vector of attack, we're going to try to identify where the cyber actors have gone on the network. We're going to look for physical evidence, hard drives and servers and we're also going to look for logs: network logs, domain logs, firewall logs, determine who had administrative privileges, how many remote access points there are to a certain network, the topography of the network, how big is your network, how many locations. Just get the whole picture of the network and then try to determine where the intrusion occurred and where they moved.
Typically in cyber intrusions they get an initial foothold, an initial vector of attack. They get on the network, then they attempt to escalate their privileges and move laterally.
How does the Cyber Division work with federal agencies to investigate breaches?
We are the lead investigative agency for cyber investigations and cyber intrusions. DHS has the lead for securing federal networks, so we work in close partnership with them and they are a member of the NCIJTF.
We also share indicators of compromise from investigations in other means available to the FBI. We're a unique agency in that we have both national security and criminal authorities. We collect information from a variety of sources to include our intelligence community partners and we can share some of that information to protect companies and obviously U.S. government agencies from cyberattacks.
Private sector companies have very sophisticated cyber security procedures, cyber threat centers, incident response teams out there. We bring a complete set of tools.
We bring the full force of the United States government, as I stated we work in close partnership with other members of the government and the U.S. intelligence community. We have a lot of threat indicators, indicators of compromise, a lot of institutional knowledge based upon all the previous computer intrusion investigations we've worked. So we bring that to the table.
Each of our 56 cyber task forces has a computer analysis response team and then nationally working in cyber operations Section IV is our cyber action team, which is a team of select experts that can also respond to major computer intrusions.
So we bring experience, we bring institutional knowledge and we bring partnership. Based upon past investigations we know what to look for. We know how certain threat actors or criminal activists or criminal enterprises have functioned on similar networks and I think we know where to look for them.
Aaron Boyd is an awarding-winning journalist currently serving as editor of Federal Times — a Washington, D.C. institution covering federal workforce and contracting for more than 50 years — and Fifth Domain — a news and information hub focused on cybersecurity and cyberwar from a civilian, military and international perspective.